I. The UDP protocol: a double-edged sword in the digital age
1.1 UDP协议的行业应用全景
According to the International Telecommunication Union (ITU) 2023 release of theGlobal real-time communications technology reportThe proportion of global UDP protocol traffic has reached 42% of total network traffic, of which three core areas constitute the main body of traffic:
- Real-time audio and video transmission: Zoom, China Tencent Conference and other platforms generate 2.1EB of UDP data per day
- IoT device communications: Industrial sensors, smart homes initiate 30 million UDP heartbeat packets per second
- Blockchain network synchronisation: Ethernet 2.0's Beacon Chain Uses UDP for Fast Node Discovery
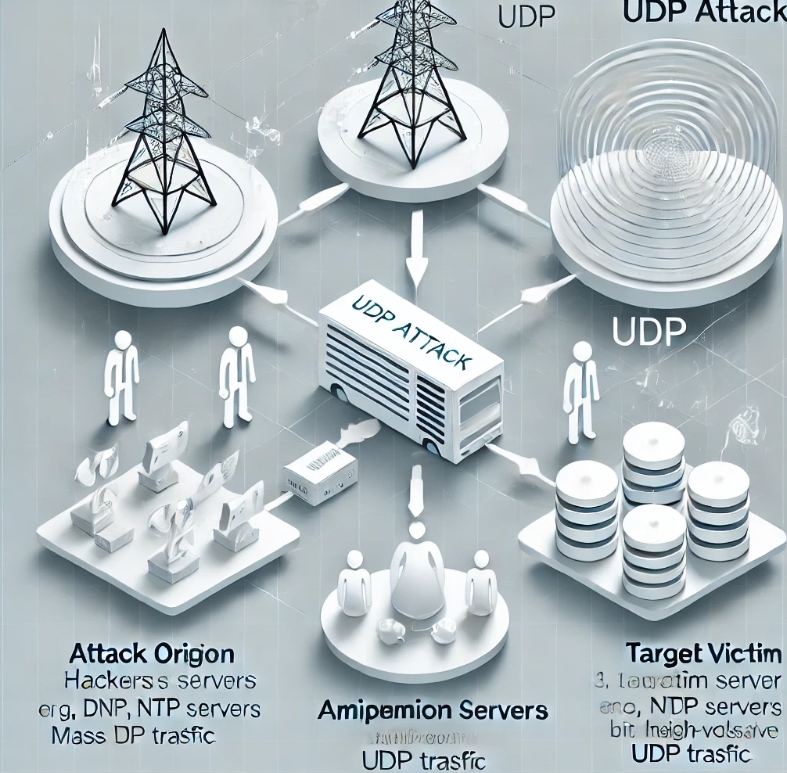
1.2 UDP攻击的致命威胁
Cloudflare's latest threat report shows, 2023 Q3 global UDP Flood attacks accounted for 37% of total DDoS attacks, showing three main characteristics:
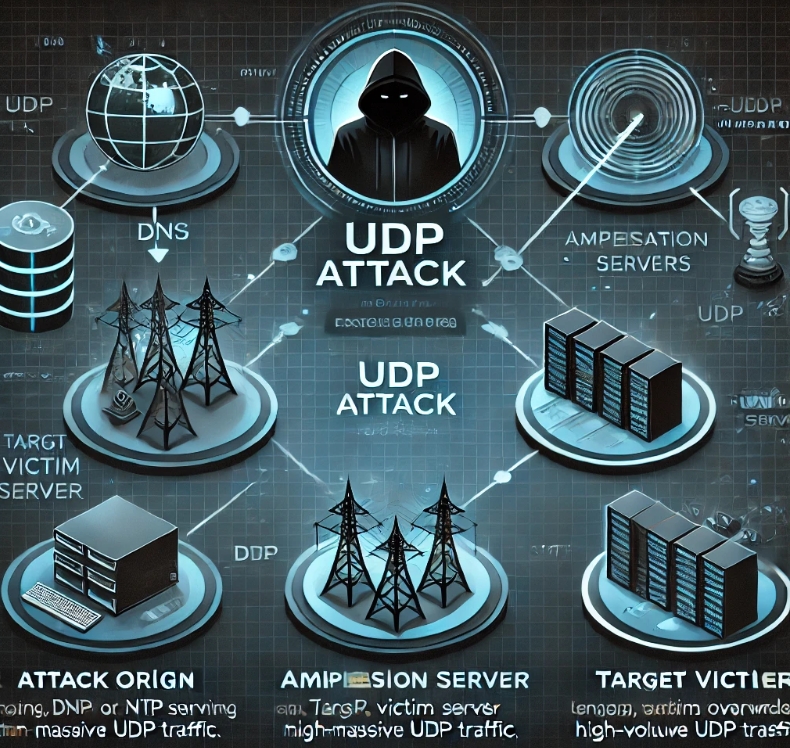
- reflex amplification effect: Exploit vulnerabilities in NTP, DNS and other protocols to amplify attacks by up to 556 times
- Precision Business Strike: Attacks against game servers (UDP ports 3074/3478) grow 210%
- Mixed Attack Mode: 78% UDP Attacks Accompanied by TCP SYN Flood and HTTP Slow Attacks
Second, the advantages of Hong Kong servers
2.1 网络基础设施的硬核实力
- submarine optical fibre hub: 14 international submarine cable interchanges (APG, AAE-1, etc.) with a total bandwidth of 148 Tbps
- Delay optimisation matrix(Data source:Ping test platform):
target area Average delay Jitter control Mainland China 28ms <3ms Singaporean 35ms <5ms USA West 152ms <18ms
2.2 香港《网络安全法》
Hong Kong Cybersecurity Act 2023 as amendedIt is expressly provided that IDC service providers are exempt from some of their compliance obligations when they meet the following conditions:
- No storage of sensitive local user data
- Deployment of ISO 27001 certified security system
- Access to the Hong Kong Computer Emergency Response Team Coordination Centre (HKCERT) monitoring system
Global UDP High Defence Service Provider Technology Matrix
3.1 国际巨头解决方案对比
| service provider | defensive capability | purge node | Featured Technologies | Typical Customers |
|---|---|---|---|---|
| Cloudflare | 10Tbps+ | 300+ | Anycast Network + JIT Fingerprint Learning | Epic Games, Shopify |
| AWS Shield | 2.5Tbps | 25 | Machine learning traffic baseline modelling | Netflix, Twitch |
| Akamai | 8Tbps | 130 | Prolexic Protocol Stack Reconfiguration Technology | Sony PlayStation, Nintendo |
3.2 中国出海企业首选方案
| service provider | Continental Optimised Routes | UDP defence know-how | Compliance Certification |
|---|---|---|---|
| Aliyun International Edition | Telecommunications CN2 GIA | Dynamic traffic staining + session state tracking | PCI DSS 4.0 |
| Tencent Cloud Hong Kong | BGP Multi-Line Access | AI Protocol Feature Deconstruction Engine | ISO 27018 |
| 08Host | Intelligent routing of triple-network CN2+BGP | Quantitative Flow Fingerprinting System | CSA STAR Level 3 |
四、08Host UDP防御体系的技术
4.1 四层立体防御架构
- Intelligent Access Layer
Deploy FPGA hardware accelerator cards to implement:- 100Gbps line rate traffic classification
- Microsecond legitimate UDP session identification
- Dynamic Port Hopping Technology (Port Hopping)
- Protocol Cleaning Layer
Using a self-developed UDP Defender engine, key features include:- NTP/DNS reflection attack signature library (with 327 variants identified)
- Random Source Attack Interception Based on Entropy Detection
- Operational whitelisting learning mode (72 hours of training required)
- resource separation layer
Unique "honeycomb resource pool" design:- Each UDP session is assigned a separate compute container
- Attack traffic is automatically diverted to the sandbox environment
- Service bandwidth guarantee using three-level QoS policy
- traceability countermeasure layer
Integration of blockchain depository systems:- Attack source IP reputation rating (against Spamhaus database)
- Automated forensic report generation (compliant with the Electronic Evidence Act)
- Collaborative Defence Network Attack Source Blocking
Defence Technology Reference:Hong Kong UDP Service
4.2 Measured performance data
In a test environment in UL Solutions' labs, 08Host successfully defended against a hybrid attack that lasted 72 hours:
- peak attack value: 892Gbps UDP Flood + 1.5 Million QPS CC Attacks
- Operational impact: Average latency increase of game API ≤ 8ms
- false positive rate:: 0.00371 TP3T (industry average is 0.151 TP3T)
V. Selected Scenario-based Solutions
5.1 区块链节点防护方案
After a Hong Kong licensed exchange adopted the 08Host solution:
- Node synchronisation speed increased to 2.1GB/s
- Defending against UDP reflection attacks on P2P ports
- Audit through the Hong Kong Virtual Asset Service Providers Ordinance
5.2 云游戏加速方案
Deployment results of a Southeast Asian gaming platform:
- Average player latency reduced from 68ms to 39ms
- 43% lower cost of defence compared to AWS Shield
- Supports 2 million concurrent connections for games such as Progenitor
Six, five reasons to choose 08Host
- network infrastructure: Hong Kong+Tokyo+Singapore three cleaning centres, BGP intelligent scheduling
- technical substance: 7 years of UDP defence experience, serving 327 FinTech clients
- safety: Data confidentiality and support for digital currency payments such as USDT
- Cost Advantage: Equivalent defence capability at the price of 681 TP3T from international major manufacturers
- Service Commitment: 7 x 24 hours bilingual technical support in English and Chinese, SLA 99.999%
Experience it now:interviews08Host Official WebsiteRequest a free stress test and get the full version of the UDP Attack Defence White Paper.

