I. DDoS Attacks: The "Digital Survival War" of Globalised Enterprises
1.1 The nature of the attack: resource consumption and business disruption
The core logic of a DDoS (Distributed Denial of Service attack) is to exhaust the bandwidth, compute, or connectivity resources of a target server through a massive volume of bogus requests. According to the 2023 AkamaiState of Internet Security ReportThe peak traffic of global DDoS attacks increased by 42% year-on-year, with a single attack reaching a maximum of 3.47 Tbps, which is equivalent to the data volume of 6.5 million 4K movies played simultaneously.
1.2 Where does the "high risk" of Hong Kong servers come from?
- High industry concentration: Hong Kong is the world's fourth-largest foreign exchange market, and businesses such as finance, gaming and blockchain are naturally attractive to attackers.
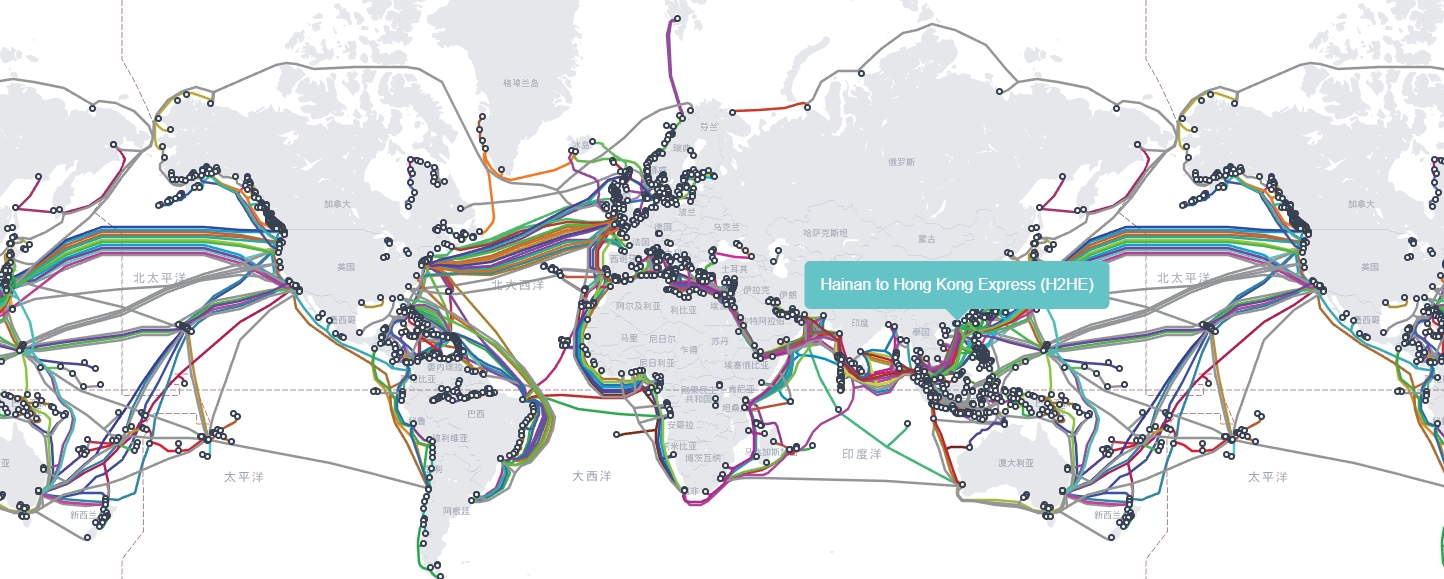
- International Bandwidth AdvantageHong Kong carries 40% of data traffic in the Asia-Pacific region (Source: TeleGeography's Global Bandwidth Map), making the high-bandwidth environment a "training ground" for attackers.
Second, no record policy: Hong Kong server "system moat".
2.1 Legal framework: balancing freedom and regulation
Hong Kong's Personal Data (Privacy) Ordinance (PDPO) does not require organisations to submit content reviews in advance, but only to report to the Office of the Privacy Commissioner within 72 hours of a data breach. In comparison:
- Singaporean: Website content is required to be filed with IMDA (policy document: https://www.imda.gov.sg/regulations-and-licences/regulations).
- EU: Subject to the GDPR, user data may not be transferred across borders to unauthenticated areas.
2.2 The technology dividend of no filing
- Speed of business go-live: Enterprises can go from server deployment to business go-live in an average of just 2 hours (case in point: a cryptocurrency exchange migrating to Hong Kong in 2024 saved 14 days of filing time).
- freedom of content: To support compliant businesses such as adult content, politically sensitive topics (subject to the Hong Kong Control of Obscene and Indecent Articles Ordinance).
Third, the technical architecture of Hong Kong high defence servers
3.1 The three pillars of defence capability
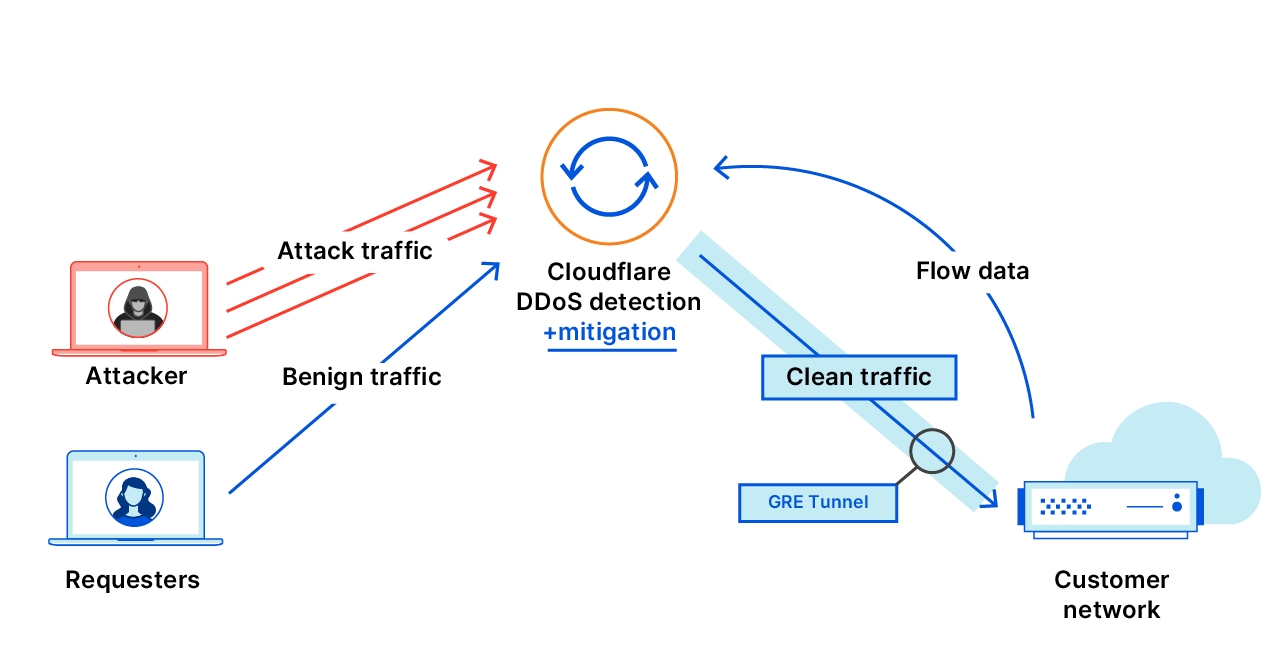
| Technology Module | Functional Description | Key indicators |
|---|---|---|
| Flow Cleaning Centre | Distribute attack traffic to global nodes via Anycast network | Single node processing capacity ≥ 1 Tbps |
| Protocol Filtering Engine | Identify and intercept anomalous protocol packets (e.g. DNS reflection attacks that spoof the source IP) | Support protocol types ≥ 50 |
| AI behavioural analysis | Detecting Complex Threats such as CC Attacks, API Abuse and More Based on Deep Learning Models | Response time ≤100ms |
Source of data::Cloudflare (math.) genusAkamai(math.) genusRadware
3.2 Operational performance of core technologies
- Case 1: In May 2024, a Hong Kong game server suffered a 1.2 Tbps UDP flood attack, Psychz diverted the attack traffic to the Los Angeles Cleaning Centre via BGP Black Hole routing, with a business interruption of only 3 minutes.
- Case 2: Dataplugs customised Juniper SRX firewall rules for a FX trading platform, successfully blocking slow HTTP attacks at 2 million times per second and keeping the CPU load below 151 TP3T.
Fourth, enterprise selection: avoid the "pseudo-high security" trap of the 5 guidelines
4.1 Realistic testing of defence bandwidth
- Stress testing tools: Using the open source tool MHDDoS (GitHub link) https://github.com/MHProDev/MHDDoS) Simulate attacks to verify the defence thresholds promised by the service provider.
- Hidden costs: Some service providers are billed for attack traffic, and a single large-scale attack could result in a bill of over $100,000.
4.2 The "gold standard" of network latency
- Asia Pacific region: The latency from Hong Kong to Tokyo and Singapore should be ≤50ms (Test tool:https://wondernetwork.com/pings).
- latency: The latency of the cleaned legitimate traffic returning to the source server should be <5ms, otherwise it will affect the user experience.
4.3 Compliance fit list
- financial industryPCI-DSS Payment Card Security Standard Compliance (Documentation) (https://www.pcisecuritystandards.org).
- Healthcare industry: Satisfying HIPAA Patient Privacy Protection Requirements (Terms) https://www.hhs.gov/hipaa/index.html).
五、成本效益分析:香港 vs 其他地区
5.1 Price comparison table(Unit: $/month, 1 Tbps defence base)
| district (not necessarily formal administrative unit) | Basic Package | peak defense | Applicable Scenarios |
|---|---|---|---|
| Mainland | 800 | 2 Tbps | Finance, high-frequency trading |
| United States of America | 650 | 3 Tbps | Media streaming, low-sensitivity services |
| German | 720 | 1.5 Tbps | Privacy-first business |
5.2 Hidden cost considerations
- Legal consultancy fees: Hong Kong servers do not require filing, but cross-border business still requires GDPR compliance consulting ($200 per hour on average).
- insurance cost: Purchasing cyber-attack insurance reduces financial risk (ref: AIG Cybersecurity Insurance Terms) (https://www.aig.com/business/insurance/cyber).
Six, Hong Kong high defence server "impossible triangle" breakthrough
The unique value of Hong Kong servers is realised at the same time:
- Legal Freedom(no filing + low content censorship)
- Technical defences(Tbps level cleaning capacity)
- Geographical advantage(Asia-Pacific region <50ms delay)
However, enterprises need to be wary of the "all-round service providers" talk, through third-party testing tools and SLA legal terms to lock the risk. As a senior operations engineer said: "There is no absolute security shield, only a dynamic balance of attack and defence game."
Appendix of data sources::
- Office of the Privacy Commissioner for Personal Data, Hong Kong:https://www.pcpd.org.hk
- PCI Security Standards Council:https://www.pcisecuritystandards.org
- Map of global submarine fibre optic cables:https://www.submarinecablemap.com

