
Why do businesses need Tether-enabled high defence servers?
When a business chooses a server, the flexibility of the payment method is just as important as the security of the server.
Scenario-based questions::
- How can cross-border business avoid the exchange controls of traditional banks?
- How do you ensure that your business is not disrupted in the event of a large-scale DDoS attack?
- Why are more and more businesses asking for a "cryptocurrency payment" option?
These questions point to an immediate need:Tether (USDT) Payment Supported High Definition Recorded ServersThe first time I saw it, it was a very good one. So today together with 08Host editorial!
I: The Business Value and Technical Logic of Tether Payments
1.1 Why do businesses choose Tether Payments?
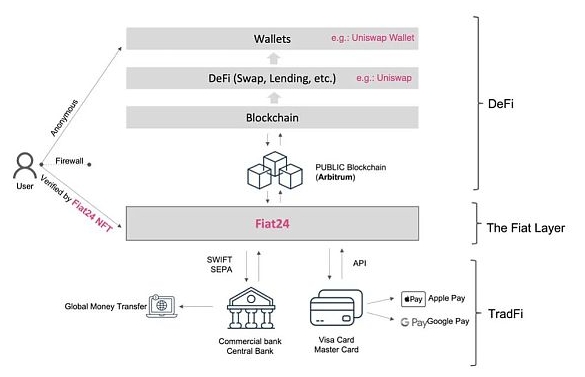
- Anonymity and privacy protection: No need to bind a bank account to reduce the risk of leaking sensitive information (refer to the official website for details):Tether White Paper).
- Zero friction in cross-border paymentsUSDT as a stablecoin to avoid exchange rate fluctuations and arrive in minutes (case in point: a Middle Eastern e-commerce platform saves 30% in fees by paying via Tether).
- Avoiding policy risks: In areas where banking services are limited (e.g. some South American and Southeast Asian countries), USDT is the only reliable payment method.
Data support::
As of early 2025, Tether (USDT) has a market capitalisation of around$82 billion around 70% share of the stablecoin market.
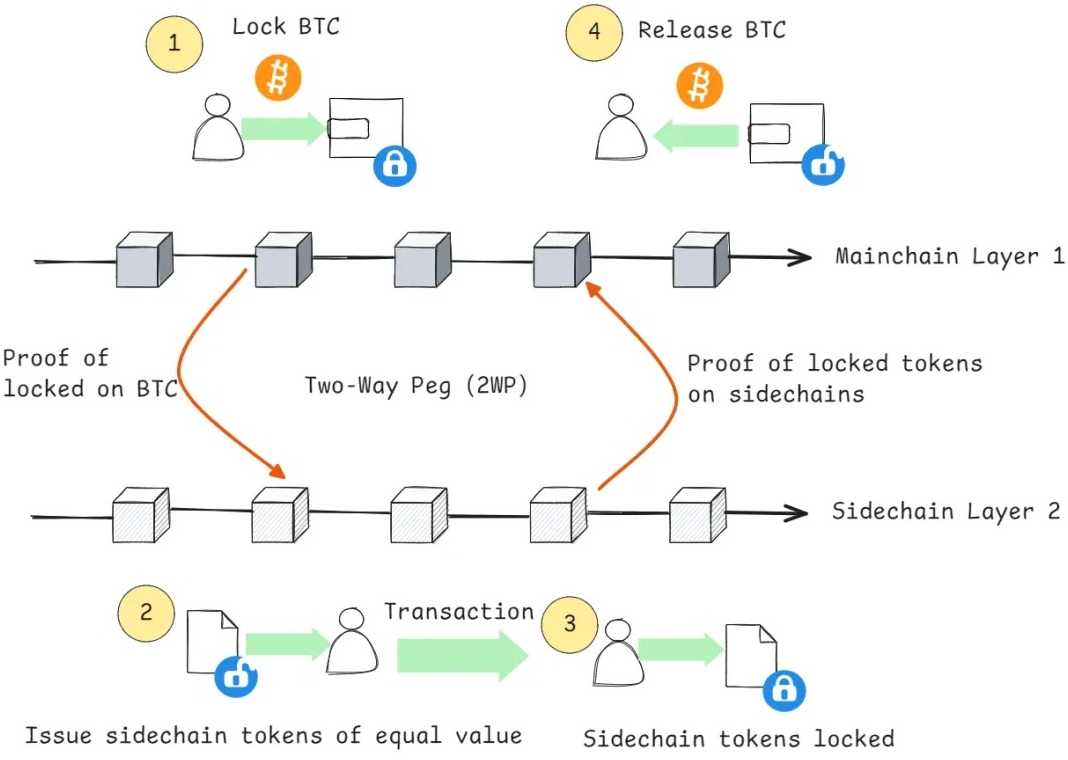
1.2 Technical implementation of Tether payments
- Blockchain Confirmation Mechanism: Server vendors access blockchain nodes (e.g., Ether, TRON) via APIs to verify transaction hashes in real time.
- Automated turn-up service: A smart contract triggers the server configuration process and deployment is completed within 5 minutes after the user pays (see Chapter 4 for technical details).
Chapter 2: The core indicators of high defence record servers
2.1 What is "High Definition Filing"?
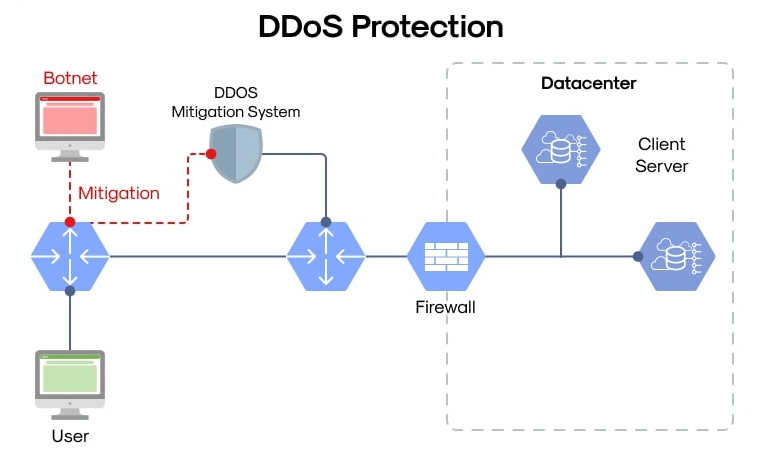
- High Defence (DDoS Protection):抵御TB级流量攻击,需具备流量清洗中心与IP黑洞路由技术。
- Filing (compliance): It means that the server is located in a region that allows hosting of sensitive businesses (e.g. finance, gaming, gambling) and meets the local data centre certification.
2.2 high defence server的技术架构
- Three-layer protection system::
- Edge Node Filtering: Identifies and intercepts anomalous traffic (e.g.SYN Flood).
- BGP line diversion: Directing attack traffic to cleaning centres.
- local hardware firewall: Set up custom rules (e.g. CC attack protection).
- real-life example: An exchange used 08Host's high defence servers to successfully defend against a 650 Gbps attack that lasted 72 hours.
Chapter 3: Recommended High Defence Service Providers Supporting Tether Payments Worldwide
3.1 Service provider selection criteria
- payment method: Explicit support for USDT (TRC20/ERC20).
- defensive capability: Provides at least 500 Gbps base protection, upgradable to T-level.
- Compliance filing: Data centres are PCI DSS or SOC 2 certified.
3.2 Recommendation List

1, 08Host
Core strengths::
- Exclusive support for "Tether Automatic Instant Activation", no need for manual review.
- 8 high defence nodes worldwide (Los Angeles, Frankfurt, Singapore, Hong Kong, etc.), with a single node defence value of 1.2 Tbps.
- Provides compliance filing support (can host cryptocurrency exchanges, online gaming).
- Applicable Scenarios: High-frequency trading platforms, multinational e-commerce, privacy-sensitive projects.
- official website::www.08host.com

2, KnownHost
Core strengths::
- US Veteran Hosting Provider
- Support USDT payment
- Defence capacity 800 Gbps.
- Official website:www.knownhost.com

3, Hostwinds
Core strengths::
- Enterprise level customised protection
- Accept Tether Annual Payment Offer
- Official website:www.hostwinds.com
Chapter 4: How to implement Tether payments with high defence services?
4.1 Payment system integration programme
- API Docking Exchange: Service providers get real-time USDT rates via Coinbase Commerce or BitPay API.
- smart contract trigger: After the user pays, the on-chain transaction hash (TXID) is automatically verified to open server privileges.
4.2 The Cost Challenge of High Defence Architecture
- bandwidth cost: 1 Tbps protection requires at least 10 backbone access points (cost ~$2000/month).
- Why 08Host can achieve low prices::
- Build your own cleaning centre to reduce third-party dependence.
- Partner with TRON Chain to reduce USDT transfer fees.
Chapter 5: How to choose the right programme for you?
5.1 Assessing business needs
- defence threshold: 500 Gbps basic package is available for average daily traffic below 50 Gbps.
- Payment preferences: Preference is given to service providers that support TRC20 (lower handling fees).
5.2 Guidelines for avoiding pitfalls
- False advertising identification: Vendors that claim "unlimited defence" but do not have the address of a specific cleansing centre are to be taken with a pinch of salt.
- Compliance verification: Require the service provider to provide the data centre certification number (e.g. 08Host Singapore node number #SG-2023-CCC).
Conclusion:
When enterprises are facing increasingly severe cyber attacks and cross-border payment barriers, choosing a service provider like 08Host that supports Tether payments and has real protection capabilities is not only a technical upgrade, but also a strategic business decision.

