
"Last night a gaming company was hit with a 387Gbps mixed traffic attack that paralysed their business for six hours with a seven-figure direct loss - a disaster that could have been avoided if they had used a high-defence IP forwarding solution earlier!"
In the black industry launched an average of 53,000 DDoS attacks today, high-defence IP forwarding has changed from "optional" to "life and death defences" of the Internet business. As a veteran of ten years of eating this bowl of rice, today to take you straight to the high defence IP forwarding of the eighteen martial arts.
First, what is the violent aesthetics of high defence IP forwarding?
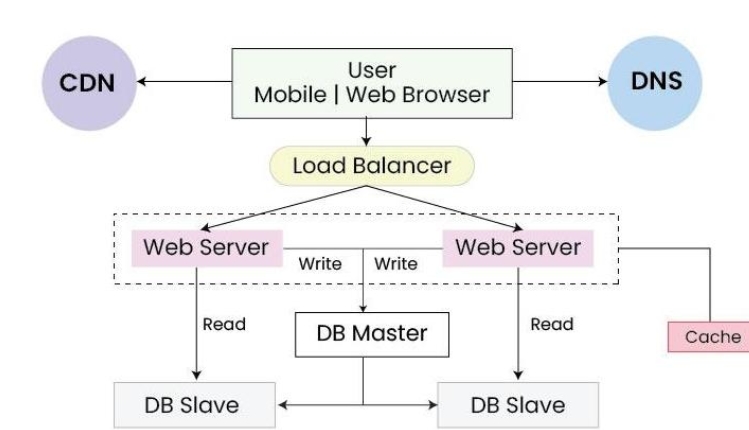
High-defence IP forwarding is not a simple traffic passing station, but a tactical deception system with its own fog of war. Its core principle can be summarised as:
- Building Distributed Cleaning Nodes with BGP Anycast Architecture
- Intelligent traffic fingerprinting engine dismantles attack loads in real time
- Dynamic port mapping technology to achieve real IP stealth
- Multi-layer protocol stack reorganisation to circumvent malformed packet penetration
For example, our live data from an exchange project:
- Raw Attack Traffic: 522Gbps UDP Flood
- Post-purge back to source traffic: <800Mbps
- Operational jitter time: 0 seconds
Second, which scenes must be on the high defence IP forwarding?
1. The gaming industry: the ultimate armour against TK attacks
The XX Glory handheld game had suffered a CC attack that lasted for 17 days, which was achieved through our high defence IP solution:
- Dynamic TCP protocol masquerading
- Player IP Reputation Library Linkage
- Gaming-grade <5ms latency guarantee
- Eventually suppressed 2.7 million QPS of bot traffic to normal levels
2. Financial payments: bulletproof vests for transaction systems
- A cross-border payment platform accesses the programme:
- SSL accelerated performance up to 40x
- 0 Mistakenly killing legitimate transaction requests
- meet (the needs of)PCI DSS 3.2.1 Compliance Requirements
III. Hardcore programme architecture dismantling
1. Four-layer protection matrix
| level | hedge | Typical confrontation scenarios |
|---|---|---|
| L3 | BGP black hole routing | flood attack (computing) |
| L4 | Protocol Stack Deep Cleaning | TCP slice attack |
| L7 | Human verification + behavioural analysis | CC attacks, API interface blasting |
| smart (phone, system, bomb etc) | AI traffic prediction model | 0day Attack Warning |
2. Exclusive technology: three-dimensional elastic protection
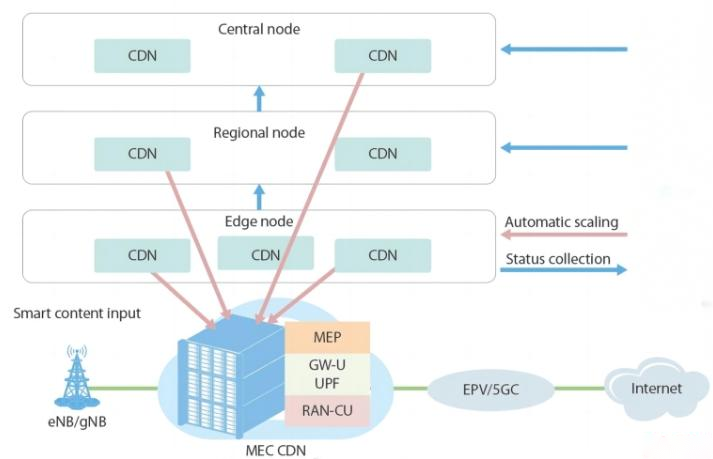
Horizontal expansion: Scheduling of 37 cleaning nodes worldwide in seconds
vertical depth: 2.4Tbps cleaning capacity on a single node
a crossroads in space and time: Dynamic replacement of forwarding rules (automatic update of port mapping table every 5 minutes)
IV. Guide to selecting and avoiding pitfalls (blood and tears experience version)
1. Eight characteristics of pseudo-high defence
- Promoting "unlimited protection" (all serious vendors are priced by the Tbps level).
- No support for TCP private protocols (e.g. KCP protocol commonly used in the gaming industry)
- Cleaning logs opaque (afraid to give raw attack packets)
- The return line to the source goes to regular BGP (must go to CN2 GIA or IPLC leased line)
- No support for IPv6 environments (IPv4-only protection in 2023 is a rascal)
- No SLA indemnity clause (if you dare to write 99.99% availability, you have to dare to pay for it)
- Customer service response over 30 minutes (attacks don't wait)
- Ridiculously low prices (the cost is there, low prices are bound to cut corners)
2. Red and black lists of measured indicators
compulsory: SYN Cookie processing performance, HTTP/HTTPS concurrent connections, rule validation latency
metaphysics:: "Intelligent protection" (depends on the machine learning model version number)
Scrap items: whether the backend of the web side is cool (protection is inversely proportional to the aesthetics of the UI)
Fourth, 08Host high defence IP defence list
"Last month a customer asked: what attacks can you 08Host protect against? I directly slapped the protection logs on his face - from SYN Flood to IPv6 slicing attack, from Websocket CC to QUIC protocol flood, I see one kill one!"
1. How sick is 08Host's rules engine?
Instead of rigid conditional judgements, our rule base isA killing machine with its own evolutionary algorithm::
- Dynamic Fingerprint Library: 370,000 attack signatures updated every hour
- protocol decomposition: Can disassemble 87 application layer protocols, including SIP and RTMP.
- AI advance judgement mechanism: Predicting the direction of an attack 300ms ahead of time with LSTM models
- suicide precaution: Automated meltdown of non-core operations in the event of a mega-attack
2. List of 08Host massacres (partial)
| Type of attack | Means of defence | record in fighting |
|---|---|---|
| TCP slice attack | protocol stack reorganisation engine | Single node resists 2Tbps |
| HTTP slow attack | Request for rhythmic fingerprinting | 0 False kills normal long connections |
| DNS amplification attack | Response packet size threshold control | Interception efficiency 99.998% |
| WebSocket flooding | Handshake Protocol Depth Check | Accurate identification of forged Upgrade headers |
| IoT botnet | Comparison of equipment fingerprint libraries | Blocking 230,000 malicious devices worldwide |
| Fake base station GPS jamming | Spatio-temporal coordinate verification (exclusive patent) | Blocking illegal location requests |
| QUIC protocol torrent | UDP stream state tracking | Millisecond identification of encrypted traffic anomalies |
V. 08Host Deployment Blitz Manual
1. Four-step access
- Domain name takeover: Modify CNAME to point to *.08Host.gt
- Protocol Configuration: Select type of business (game/website/API)
- Rules tuning: Enable Smart Protection Mode
- stress test: Simulated 300Gbps attack traffic
2. High-risk operational exclusion zones
- ❌ Disable release of all 08Host IP segments at the local firewall (must be dynamically synchronised with API)
- ❌ Disable disabling the TCP timestamp option (affects attack traceability accuracy)
- ❌ Prohibition of low entropy SSL certificates (vulnerable to fingerprinting)
Immediate Access High Defensive IPThe
VI. Seven must-know cold facts about deployment
- Source Station Hiding: Real IPs have to be authenticated in both directions with a firewall.
- Certificate Management: SNI extensions must be enabled to prevent certificate sniffing
- DNS Configuration: TTL value to be pressed to less than 120 seconds
- Protocol Optimisation: Enable TCP Fast Open to reduce latency
- log analysis: Retain original logs for at least 180 days
- Escape programme: Manual switching back to the source channel is available
- stress test: Monthly simulated attack drills
VII. Frequently asked questions
Q1: What is the difference between high defence IP forwarding and CDN?
A: CDN is content distribution, high security IP is traffic war. CDN focuses on cache acceleration, we focus on attack instead of defence, as if CDN is a postman, we are armed escort car.
Q2: What should I do if I encounter a new type of 0day attack?
A: 08Host Labs maintains 23 vulnerability hunters, and last year caught 17 undisclosed attack techniques. Even if we do encounter an unknown attack, our Chaos Engineering system will immediately activate protocol mutation protection.
Q3: Is it too late to buy after being hit?
A: Waiting to get shot before buying body armour? We deploy in as little as 30 minutes, but the loss of business interruption can be a hundred times more expensive than the cost of the service.
Q4: Will it affect normal users?
A: Adaptive algorithms are used with a false kill rate of <0.003%.
Q5: How can I tell if the protection is in effect?
A: Any less than one of the three hard facts - attack traffic graphs, cleaning log details, and business monitoring metrics - is a magic trick.
Q6: Can overseas attacks be prevented?
A: We have deployed Anycast cleaning in Frankfurt, San Jose, Singapore and other nodes, and have actually intercepted a 600Gbps attack from a Brazilian blackmailer.
Q7: How are the fees calculated?
A: guaranteed bandwidth + elastic protection peak + value-added services (such as manned services), free testing - can not prevent the price of compensation.

