With cyber-attacks becoming increasingly frequent, many businesses and individual webmasters are looking for cloud servers that offer high defence capabilities without the cumbersome filing process. At the same time, theUSDT (Tether) PaymentsIt has become an increasingly popular payment method due to its anonymity, efficiency and global applicability.USDT Payment for filing-free high security cloud serversCombining these two advantages, it is particularly suitable for industries such as cross-border e-commerce, gaming and fintech.
Why choose USDT Payment Free High Definition Cloud Server?
1. Advantages of USDT payments
USDT, as a stablecoin, is anchored to the United States Dollar (USD) and has the following significant advantages:
- anonymity: No need to bind a bank card or identity verification to protect privacy.
- fast settlement: Cryptocurrency transactions are fast and payments are usually completed within minutes.
- Globally applicable: Circumvent international payment restrictions, no need to worry about credit card or bank restrictions.
- inexpensive: USDT transaction fees are lower than traditional payment methods.
2. Advantages of record-free cloud servers
In mainland China, web servers are usually required to submit an ICP 备案, and choosing the Hong Kong, Singapore, USA, EuropeCloud servers in such areas can avoid the filing process and have the following advantages:
- Rapid deployment: No filing is required and can be used immediately after purchase.
- Cross-border application: Suitable for foreign trade, e-commerce, finance and other international business.
- Higher degree of freedom: No content censorship, suitable for a wide range of application scenarios.
3. Advantages of high defence cloud servers
High-defence cloud servers are mainly for DDoS, CC attacks and other malicious traffic Provide defence for high risk operations, for example:
- Financial payments(Preventing traffic attacks from paralysing payment systems)
- game server(Preventing competitors from attacking and causing players to drop out)
- cross-border e-commerce(to prevent malicious crawlers from affecting site speed)
- Cryptocurrency Trading Platform(Guaranteeing stable access)
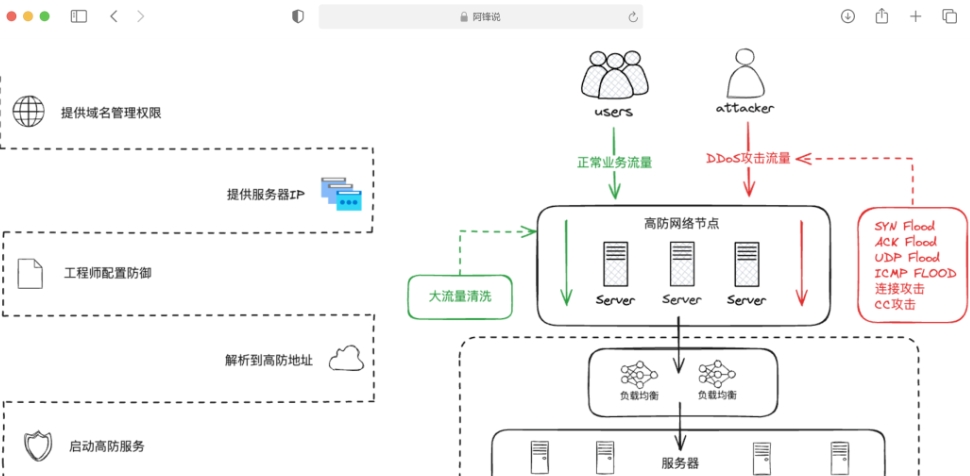
Three.How high defence servers work
The current common DDOS attack is a distributed denial of service attack (full name: Distributed denial of service attack), also called a flood attack, the so-called flood, it is raging, continuous. As the main popular means of network attack, its main idea is to make the attacker using distributed reasonable service request to make the target resources, network bandwidth exhaustion, resulting in the target can not provide normal service request.
That is to say that DDoS attacks during this time, increasing the number of abnormal visits, so that the target crashed or paralysed. To give a very graphic example, such as during the double eleven, due to the number of visitors, Taobao website paralysed look.
In addition CC (ChallengeCollapsar, Challenge Black Hole) attack is a type of DDoS attack, the principle of which is to use a proxy server to send a large number of seemingly legitimate requests to the victim server.CC attack is that the attacker controls certain hosts to send a large number of packets to each other's servers non-stop to make the other party server resources exhausted, resulting in the wastage of server resources, and the CPU Utilisation rate for a long time in the 100%, there will never be a connection that can not be processed, the network is abnormally congested until the downtime crash.
High-defence servers are mainly by the resources of the defence of hard shoulder, like someone to hit you, you go to buy a few knives and then wear a suit of armour to raise a shield to defend themselves. In practice, we need to do is: First, in the IDC server room export capacity expansion bandwidth, such as from 100G expansion to 600G or even higher, of course, these need to configure high-end router equipment, as well as the network operator's line resources as support. Secondly, the firewall equipment deployed at the exit of the server room needs to be gradually upgraded, as if in front of the server to add a shield.
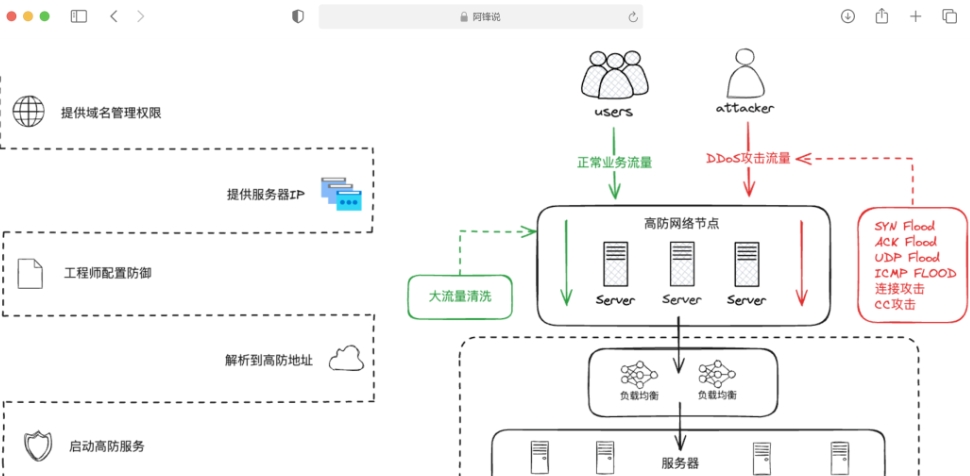
"NetShield Server was created to meet these rigid requirements. If the attack exceeds the exit of the server room, for example, the exit of the server room is 200G, ushered in an attack of up to 600G traffic how to deal with it? At this time it is necessary to operators in the server room exit with the upper layer of traffic traction technology, the normal traffic and attack traffic to distinguish, and with the attack on the traffic traction to the server room has the ability to defend the firewall equipment to go, rather than choosing their own hard to carry. It is like your own protective equipment is complete, set up a lot of roadblocks or hidden weapons in the enemy must pass through the road, first consume part of his energy, it is like as a false target to pull some of the attack traffic over.
Second, the technical analysis: how to build high-defence cloud servers?
1. Server architecture design
Usually.High Defence Cloud Server ArchitectureThe following key components are included:
- DDoS protection system: Filter malicious traffic using firewalls, traffic cleansing, IP blacklists, etc.
- Web Application Firewall (WAF): Defend against threats such as SQL injection, XSS attacks, malicious crawlers, and more.
- CDN Acceleration: Reduce source station stress and increase access speed through globally distributed caching.
- Anycast BGP Line: Provides low-latency, high-availability network transmission.
- Automated Monitoring and Alerting: Analyses traffic in real time and automatically enables defence policies when anomalies are detected.
2. Server defence code example
(1) Nginx-based CC Attack Defence
http {
limit_req_zone $binary_remote_addr zone=one:10m rate=10r/s;
server {
location / {
limit_req zone=one burst=20 nodelay;
proxy_pass http://backend_server;
}
}
}This code sets the Rate limit of 10 requests per secondThe system can be used to make 20 requests at a time, and allows for instantaneous bursts of 20 requests.
(2) DDoS defence using iptables
# Limits the number of simultaneous connections to a single IP.
iptables -A INPUT -p tcp --syn --dport 80 -m connlimit --connlimit-above 50 -j DROP
# Blocks large number of requests in a short period of time
iptables -A INPUT -p tcp --dport 80 -m hashlimit \
--hashlimit 100/sec --hashlimit-mode srcip --hashlimit-name http_limit -j ACCEPTThis rule prevents a single IP from sendingtoo many concurrent connectionsThe following is an example of a DDoS attack.
(3) Automatic blocking of malicious IPs (fail2ban configuration)
[nginx-badbots]
enabled = true
filter = nginx-badbots
logpath = /var/log/nginx/access.log
action = iptables-multiport[name=BadBots, port="http,https"]
bantime = 3600
findtime = 600
maxretry = 10fail2ban will automatically detect Nginx Access LogIf an IP is found to be accessed unusually frequently within a short period of time, the IP will be blocked. 1 hour.
III. Applicable Scenarios and Suggestions for Selection
1. Applicable scenarios
USDT Payments filing-free high defence cloud servers are suitable for a number of industries, including:
- Financial payment systems(digital currency transactions, cross-border payments)
- game server(Protection against plug-in attacks, DDoS attacks)
- cross-border e-commerce(Stable access for users worldwide)
- Film and television, streaming media(Prevent crawlers from stealing chains and increase playback speed)
2. Recommendations for server selection
| parameters | Recommended Configurations |
|---|---|
| CPU | 8 cores or more |
| random access memory (RAM) | 16GB or more |
| bandwidths | BGP 10Mbps - 1Gbps Defence Bandwidth |
| DDoS Defence | 100Gbps+ Cleaning Capability |
| stockpile | SSD NVMe High Speed Storage |
| reticulation | Anycast BGP Low Latency |
If more defence capability is required, you can choose T3+ level server room, supporting larger scale traffic attack defences.
USDT paid filing-free high defence cloud servers withPayment flexibility, andNo Filing Advantagerespond in singingStrong defensive capabilities, has become the best choice for many industries. ByNginx, iptables, fail2ban, etc.It can effectively improve the security of servers against DDoS and CC attacks.
If you are looking forStable, secure, high defencecloud servers and would like to use the USDT for paymentRecommended choicesHigh-defence cloud servers in Hong Kong, Singapore, the United States and other regionsEnsure the stable operation of the business.

