在当前数字化时代,网络安全已成为企业和个人不可忽视的重要课题。随着DDoS(分布式拒绝服务)攻击手段不断升级,...
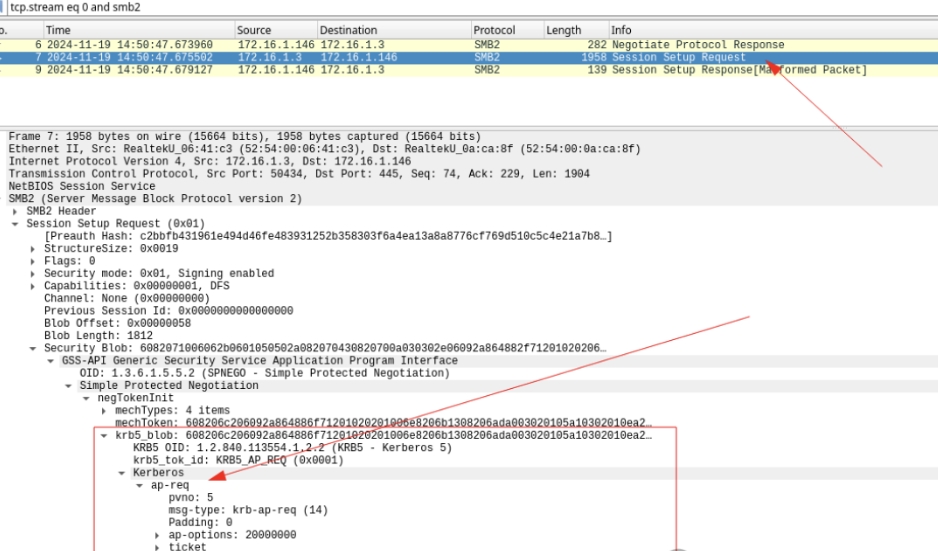
前言 我们在《Kerberos Relay 概述》中大致介绍了 Kerberos Raly 的相关概念,在《高...
我们在《Kerberos认证的基础流程(客户端获取TGT、服务票据等)》中大致介绍了 Kerberos Ral...
Kerberos 认证 这是一个老生常谈的话题,我们总能在各种各样的平台上看见关于Kerberos认证流程的解...
网络安全是系统性工程,网络设备作为关键基础设施,面临多样化的攻击威胁。尤其在高防服务器和CDN场景中,设备安全...
一、为什么「免备案」是香港服务器的卖点? 在中国大陆,工信部要求所有境内服务器必须完成ICP备案(《互联网信息...
First, Hong Kong high defence from "broiler flood" to "technical involution" of the five years of great changes 1,202...
First, understand the nature of DDoS attacks Step 1: the network ecosystem in the normal state When the business system is in a healthy state: Traffic characteristics: in line with the business model...
In 2023, the peak traffic of global DDoS attacks exceeded 3.47 Tbps, while in 2024, data from the China Information and Communications Technology Institute (CICT) showed that 60% of SMEs...
In network security, fingerprinting is a technique for identifying the type, version, configuration, and other details of a target system or service by analysing information about its characteristics. Fingerprint detection is usually...