In the age of the digital economy, cyberattacks have become one of the biggest threats to the digital transformation of organisations. According to Cybersecurity Ventures...
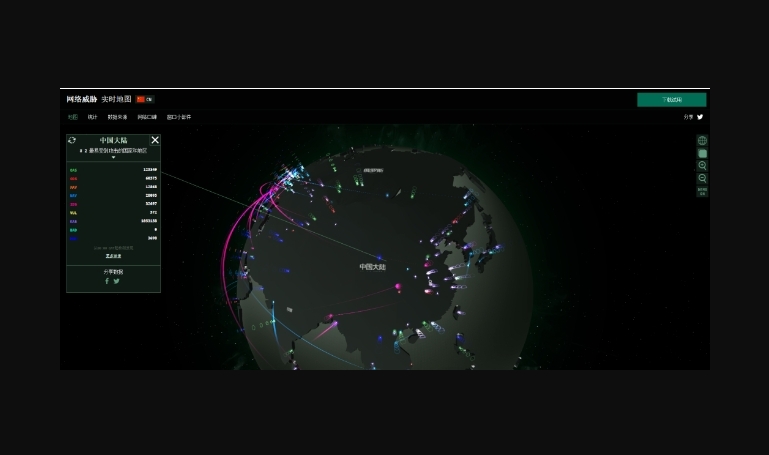
The Cyber Threat Map is one of the most attractive real-time visualisation tools in the cybersecurity field, and has evolved from an early "cool tool" to a mature "visual situational awareness...
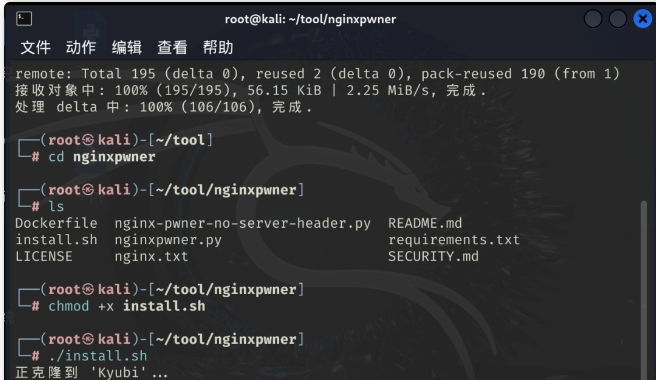
Breaking into an intranet environment is a challenging task in penetration testing, especially when the target host does not have direct access to the external network. In this case, the attacker needs to...
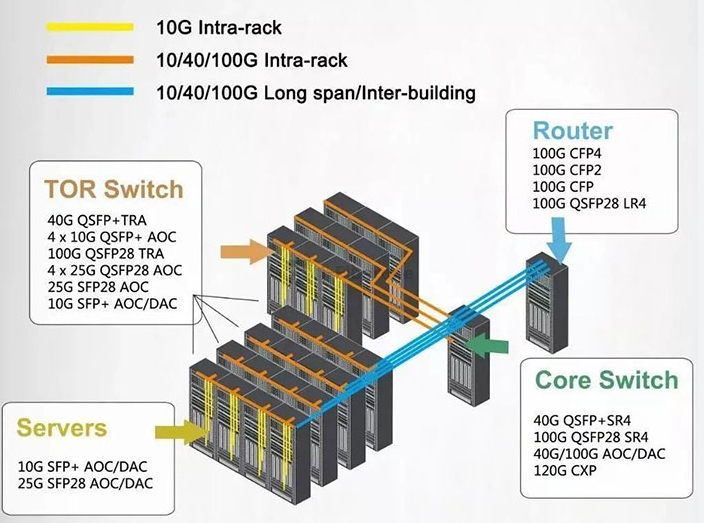
In the era of high-speed transmission of information, optical modules as a network device in the "invisible bridge", bear the core task of photoelectric signal conversion. Whether it is home broadband, enterprise...
Nginx is a lightweight, high-performance HTTP server, reverse proxy server and email (IMAP/POP3) proxy server. It ...
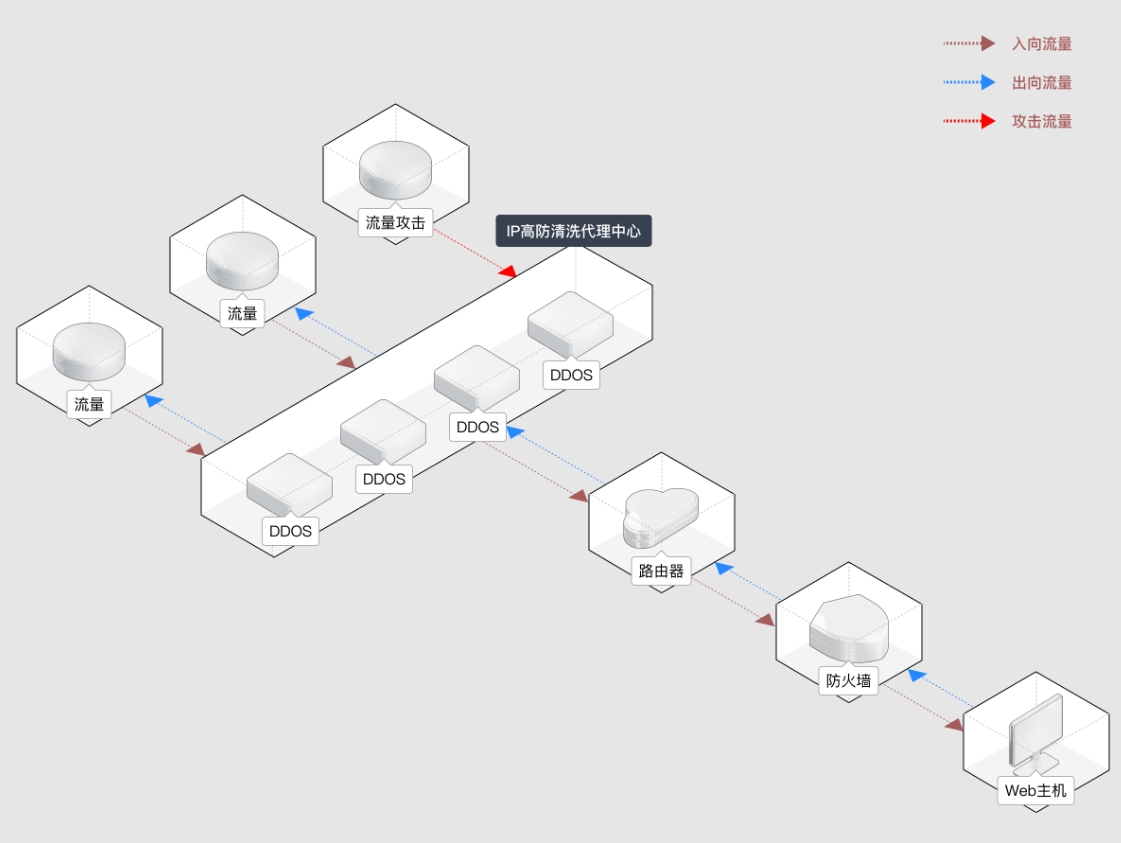
First, why cross-border business needs "no record high defence CDN"? Foreign companies conducting digital business in mainland China often face double...
Enterprises have upgraded their requirements for network infrastructure from "functional" to "efficient, secure and stable". Especially in the face of global business layout and increasingly complex network attacks...
I. Four Core Challenges for Global Enterprises Entering Mainland China in 2025 1. Policy Compliance: Continued High Pressure on the Filing System Mainland China's Ministry of Industry and Information Technology (MIIT) has a strong focus on domestic service...
In the wave of globalised digital economy, the choice of servers has a direct impact on the stability of an enterprise's business and its ability to expand in the market. Hong Kong, as an important Internet hub in the Asia-Pacific region...
The cryptocurrency space continues to thrive in the surging digital wave of 2025, with USDT as the dominant stablecoin seeing a lot of trading activity. And with...